Table of Contents
- The Real Cost of Account Sharing
- Why Max-Connections Does Not Work
- Why IP Locking Does Not Work
- Why Concurrent Stream Limits Fail
- How Abusers Share Accounts (the Real Patterns)
- The ActiveCode Protocol
- How ActiveCode Works in Practice
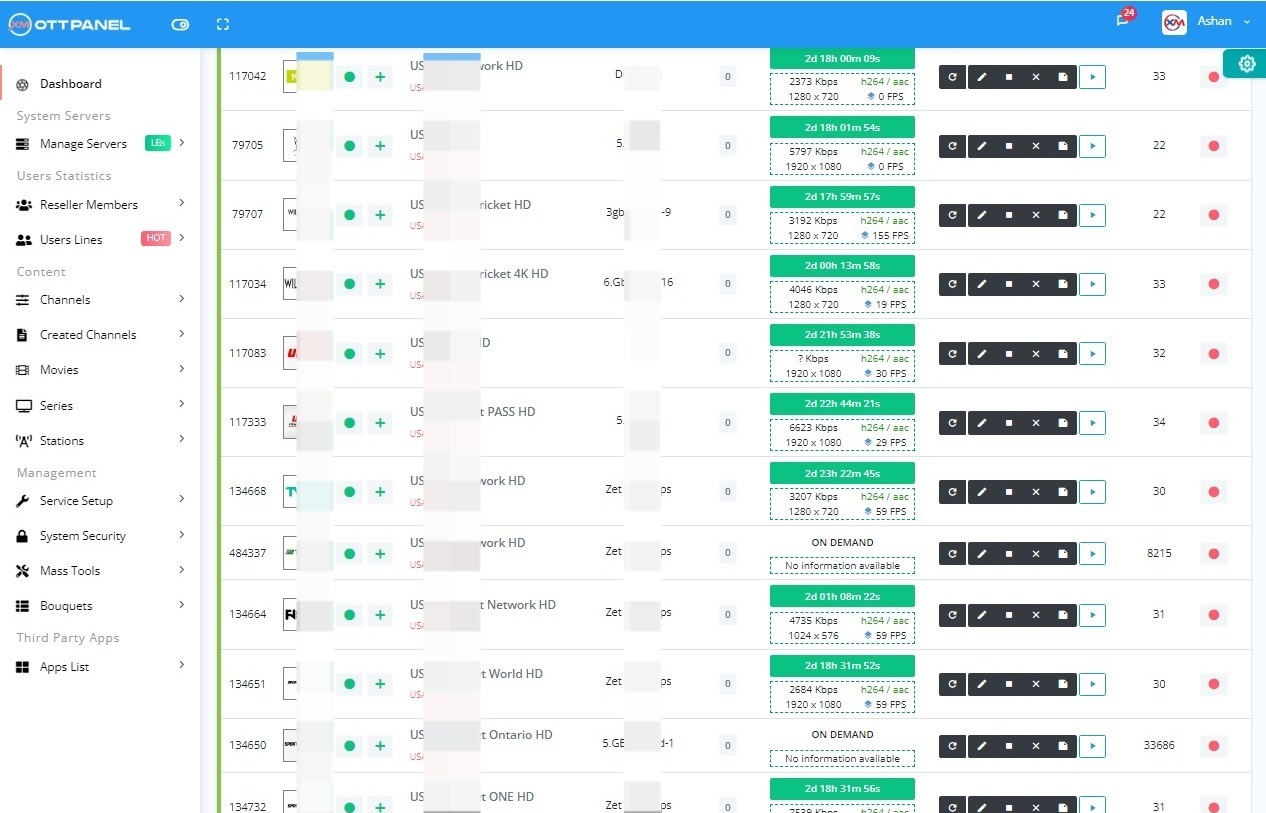
- Integrating ActiveCode in Your Panel
- Other Approaches (What They Cost You)
- FAQ
The Real Cost of Account Sharing
A serious IPTV operator with 1000 lines typically has 10-25 percent of those lines being shared across 3-5 devices each. That means the panel is actually serving 1500-2500 concurrent viewers, not 1000. The operator is paying bandwidth for all of them, but only collecting revenue from 1000.
Worse, shared accounts drive churn - the genuine paying subscriber shares with friends, the friends stop paying, the subscriber eventually asks “why am I paying when X is free for everyone” and churns too. The per-user cost skyrockets and retail pricing becomes a race to the bottom.
Every serious IPTV operator eventually has to solve this. The question is how.
Why Max-Connections Does Not Work
Every XC-family panel has a “max connections” field on each user line. Set it to 1 and in theory only one device can stream at a time.
In practice, this fails because:
- Streaming is stateless. An HLS client requests a new segment every 6 seconds, but the panel does not know if it is the same client as the last segment. Two people in different houses can alternate segments and stay under max_connections = 1.
- Family exception fallacy. “Give customers 2 connections for the living room + bedroom” ends up being 2 connections for customer + friend.
- Bouncing. When one device disconnects, another can reconnect. Fast connection cycling trades places without ever violating the cap.
Max-connections is a speed bump, not a wall.
Why IP Locking Does Not Work
Lock a line to a single source IP and it breaks for everyone who:
- Switches between home Wi-Fi and mobile data
- Uses a VPN (many IPTV customers do)
- Is behind a carrier-grade NAT that rotates IPs
- Travels
Support tickets pile up immediately. Most operators who try IP locking disable it within a week.
Why Concurrent Stream Limits Fail
A smarter variant tracks concurrent unique streams and kicks excess ones. It works somewhat better than raw max-connections, but:
- It still cannot tell two devices apart if they hit the same segment URL sequentially.
- It generates angry support tickets when legitimate users are kicked off by their own second device.
- It can be defeated by Xtream Codes reseller proxies that pool requests.
How Abusers Actually Share Accounts
Four patterns we see in the logs across thousands of panels:
Pattern 1: The Family Pool
Customer shares credentials with 3-4 family members or close friends. Each uses a single device. Connection count stays under max at any given moment because people use the service at different times.
Pattern 2: The Reseller Bypass
A low-tier reseller under your platform sells 100 “access” slots to a wholesaler. Each of those slots is actually one account shared 5 ways. The reseller makes money, the wholesaler makes money, you lose.
Pattern 3: The Xtream Proxy Server
A community runs a public Xtream proxy that aggregates user requests behind a single IP. Your panel sees 1 connection, the proxy serves 50 viewers.
Pattern 4: The Credential Forum Leak
Credentials posted on a public forum. Hundreds of random viewers try the same user/pass. Your panel shows wild connection counts during peak events.
Max-connections addresses pattern 1 weakly and nothing else. You need a protocol that ties the stream to the device, not to a username.
The ActiveCode Protocol
ActiveCode is a device-activation protocol that binds a user account to a specific client device (or small set of devices) through a cryptographic handshake during first use. Instead of authenticating with just username+password on every stream request, the client also presents a signed device token.
The protocol flow:
- User enters credentials in their client app for the first time.
- App generates a device ID (hardware fingerprint + random nonce) and sends it to the panel.
- Panel responds with an ActiveCode (signed, expires, tied to that device ID).
- On every subsequent stream request, the app presents both credentials AND the ActiveCode.
- Panel verifies the ActiveCode signature and checks it matches the originating device.
- If a second device tries to use the same credentials, it gets a different ActiveCode - and both devices' ActiveCodes cannot be valid at the same time.
Configurable per user: how many devices are allowed, how long ActiveCodes last, whether the user can manually revoke devices from their cPanel.
How ActiveCode Works in Practice
On the Panel Side
The panel stores per-user:
When a stream request arrives:
On the Client Side
Generic IPTV apps (Smarters, TiviMate, IBO Player) need to be taught the ActiveCode handshake. A panel that ships ActiveCode provides either a branded fork of the common apps, or a library/SDK that can be bolted into apps.
The Xtream-Masters ActiveCode IPTV Player App is this client. See the ActiveCode app.
Integrating ActiveCode in Your Panel
If you are on XUI.ONE, Xtream UI, or legacy Xtream Codes, you cannot add ActiveCode. The protocol needs to be integrated deep in the request pipeline, not as a PHP plugin. This is one of the reasons operators who take anti-sharing seriously migrate to Xtream-Masters.
On Xtream-Masters, enabling ActiveCode is a per-package toggle:
- Go to Management → Packages → Edit Package.
- Toggle ActiveCode required ON.
- Set Max devices per user (typical: 2).
- Set ActiveCode TTL (30 days is common).
- Save.
Users on packages with ActiveCode enabled must use the ActiveCode-aware client app. Their existing generic-XC-API apps will not work, which is by design - this is how you force the device binding.
Other Anti-Sharing Approaches and What They Cost You
- Device fingerprinting without activation - useful signal, but a passive fingerprint can be replayed by an attacker who captures it once. Not sufficient alone.
- Geolocation alerts - trigger an account freeze when the same user suddenly appears in two countries. Helpful as a fraud signal but angers legitimate travelers.
- Concurrent unique-IP detection - kick users whose credentials are seen from 3+ unique IPs within an hour. Lower false-positive rate than IP locking but still catches VPN users.
- M3U URL rotation - rotate the user's stream URL weekly; they re-fetch from cPanel. Stops casual sharing. Falls short against forum-posted credentials.
Combine these with ActiveCode for defense in depth. No single measure is perfect, but the combination drops account abuse from 20-25 percent to under 3 percent in our customer deployments.